
La maintenance des systèmes de production se positionne comme une pierre angulaire de la compétitivité et de la pérennité des entreprises. Face à cette réalité, […] Read More

La maintenance des systèmes de production se positionne comme une pierre angulaire de la compétitivité et de la pérennité des entreprises. Face à cette réalité, […] Read More

L’expérience d’un étudiant étranger dans un pays francophone peut être enrichissante sur le plan académique, culturel et personnel. Cependant, cela présente également son lot de […] Read More
Au cœur de l’innovation pédagogique, les énigmes s’imposent comme un levier fondamental pour dynamiser l’enseignement des mathématiques. En effet, loin d’être de simples divertissements, elles […] Read More

Pour diverses raisons, de nombreux lycéens envisagent de continuer les études dans une autre ville ou un autre pays après le bac. Quitter sa zone […] Read More
Vous êtes à la recherche d’un emploi ou vous candidatez pour intégrer une grande école et vous devez fournir un CV. Bien que la méthode […] Read More

Dans le monde dynamique de l’immobilier, la réussite d’une agence dépend en grande partie de la compétence et de la performance de ses agents. Afin […] Read More

De tout temps, l’éducation façonne non seulement les individus, mais aussi les sociétés dans leur ensemble. Vous vous demandez peut-être, comme beaucoup d’autres, quel est […] Read More

Travailler avec un cabinet de recrutement présente de nombreux avantages. Grâce à leur expertise sectorielle approfondie, leur accès privilégié à un large vivier de talents […] Read More

Le salaire d’un livreur Uber Eats est variable et dépend de plusieurs facteurs. En tant que travailleur indépendant payé à la tâche, ses revenus sont […] Read More

Dans un contexte où les coûts de l’éducation supérieure ne cessent de grimper, l’option d’un prêt étudiant à taux zéro se présente comme une bouffée […] Read More

Bienvenue dans notre exploration détaillée des rémunérations dans le secteur pénitentiaire, un domaine souvent méconnu mais essentiel pour comprendre les dynamiques de ce métier spécifique. […] Read More

L’orientation professionnelle est un processus complexes, semé d’interrogations. Quel métier me conviendrait le mieux ? Quelle formation entreprendre pour y accéder ? Comment trouver un […] Read More

En tant que professionnels passionnés par l’univers de l’emploi et de l’entreprise, nous avons observé une tendance croissante vers l’utilisation de solutions digitales pour faciliter […] Read More

Plongeons-nous dans l’univers de Maria Montessori, une visionnaire qui a transformé la manière dont nous percevons l’éducation. À travers cette exploration, nous détaillerons les principes […] Read More

Le coaching fait aujourd’hui partie des éléments clés pour aider les entreprises à améliorer leur performance, développer leur potentiel et atteindre leurs objectifs. En travaillant […] Read More

Le domaine de la finance est souvent perçu comme prestigieux et lucratif, suscitant des rêves et des aspirations chez de nombreux jeunes professionnels. Cependant, la […] Read More

En entreprise, il est toujours utile de proposer des formations sur le terrain et d’évaluer régulièrement l’efficacité de la formation. Les équipes commerciales font partie […] Read More

Le monde numérique évolue rapidement et offre de nombreuses opportunités pour le développement rural. Les technologies numériques telles que l’Internet, les téléphones mobiles, les ordinateurs, […] Read More
Dans cet article, nous allons explorer comment ChatGPT, un générateur de texte IA basé sur la technologie GPT-3.5, utilise l’IA pour générer des réponses efficaces. […] Read More

En tant qu’étudiant, entreprendre peut être un défi, mais c’est une opportunité incroyable pour développer des compétences en leadership, en gestion de projet et en […] Read More

Les avancées technologiques telles que l’Intelligence Artificielle (IA) ont considérablement évolué ces dernières années, et ont apporté de nombreux changements dans notre vie quotidienne. Avec […] Read More

En France, l’éducation est très valorisée, et les parents cherchent toujours les meilleures options pour l’éducation de leurs enfants. Les écoles internationales, connues sous le […] Read More
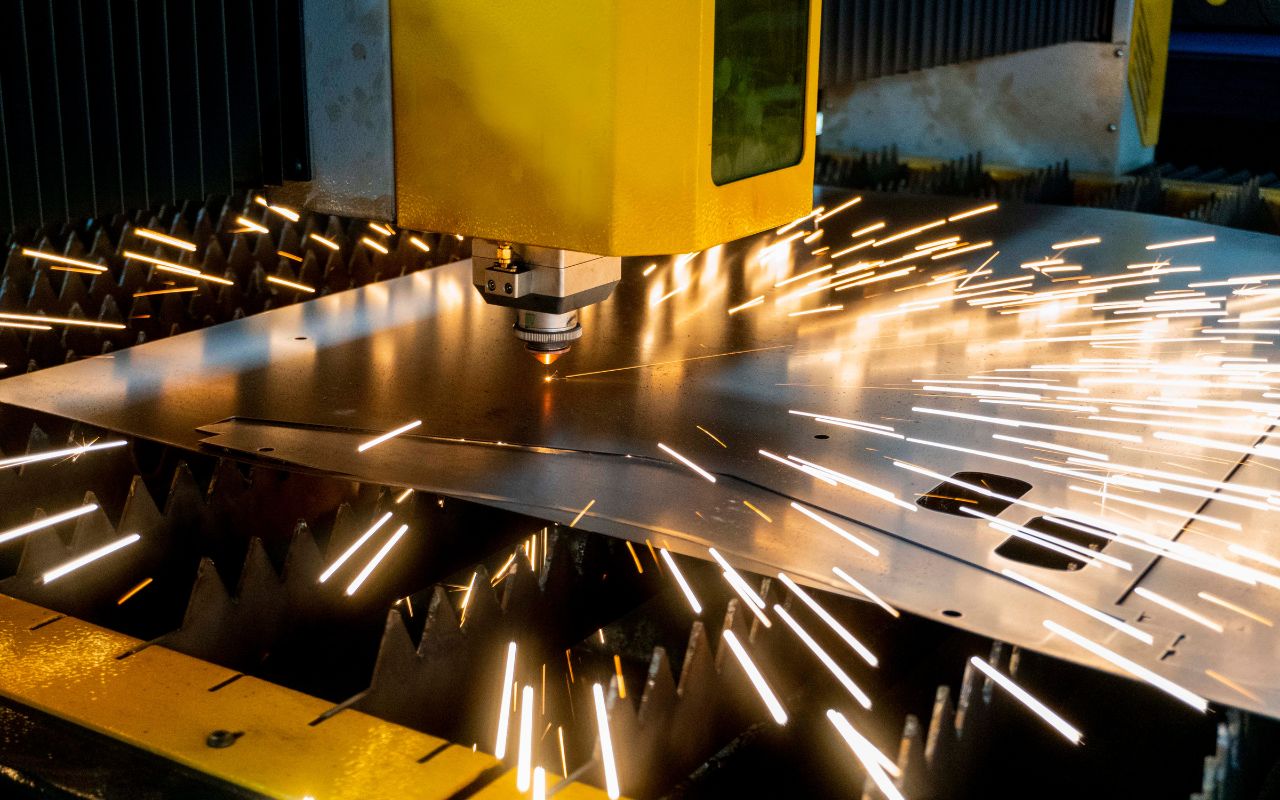
Dans un monde de plus en plus connecté et automatisé, l’industrie manufacturière a connu une croissance exponentielle au fil des années. Avec l’évolution rapide de […] Read More

L’école à la maison est une option qui a gagné en popularité ces dernières années, mais avec la pandémie de COVID-19, elle est devenue une […] Read More
Introduction Les chatbots d’IA sont de plus en plus populaires dans divers domaines d’activité, y compris la recherche en ligne. Avec la montée en puissance […] Read More

Les talibans, qui ont pris le contrôle de l’Afghanistan en août 2021, ont restreint l’accès des femmes à l’enseignement universitaire. Cette décision est un coup […] Read More
Si vous souhaitez apprendre une nouvelle langue, l’espagnol est une excellente option. Avec plus de 500 millions de locuteurs dans le monde, il est parlé […] Read More

L’Université Kean a été désignée par la National Security Agency comme Centre national d’excellence académique en cyberdéfense pour ses programmes et pratiques académiques visant à […] Read More

De plus en plus de travailleurs recherchent une flexibilité dans leur emploi, avec la possibilité de travailler à distance ou de choisir leurs horaires de […] Read More

Que vous soyez un amateur de champignons ou un chercheur en herbe, étudier les champignons est une activité passionnante et enrichissante. Cependant, comme pour toute […] Read More

Recevoir une bourse d’études peut être une véritable aubaine pour les étudiants qui souhaitent poursuivre des études supérieures mais qui n’ont pas les moyens de […] Read More

Le salon de l’agriculture est l’un des événements les plus importants pour l’agriculture en France. Ce salon est non seulement destiné aux agriculteurs, mais également […] Read More

Les subventions pour les collèges sont un moyen important pour les établissements d’enseignement de financer des projets et des initiatives qui améliorent la qualité de […] Read More

Le transport de marchandises est un élément essentiel pour toute entreprise souhaitant réussir dans le commerce et l’industrie. La capacité de transport de marchandises est donc une […] Read More

Vous souhaitez intégrer le domaine de la logistique et devenir un professionnel polyvalent ? La formation CACES FormaLogistics est faite pour vous ! Découvrez tout ce que […] Read More